It is 3:00 AM on a Saturday. Your phone vibrates on the nightstand. It is your lead developer, and they sound completely breathless.
“The cloud servers are locked. All of them. There is a text file demanding $250,000 in Bitcoin, or they delete our entire customer database.”
In that split second, your stomach drops. The blood drains from your face. You are not just thinking about the ransom money; you are thinking about the years of deep trust you built with your clients vanishing overnight. You are thinking about the crushing legal fees. You are thinking about the potential end of your business.
Founders constantly ask us if their enterprise cloud infrastructure is truly safe. The harsh reality is that the cloud is simply someone else’s computer, and automated hackers are targeting it relentlessly every single minute.
But I want you to take a deep breath. Imagine if, at 2:59 AM, a silent guardian had noticed the very first file being maliciously encrypted, and instantly cut the connection. What if it sacrificed one single server to save your entire network, completely without human intervention?
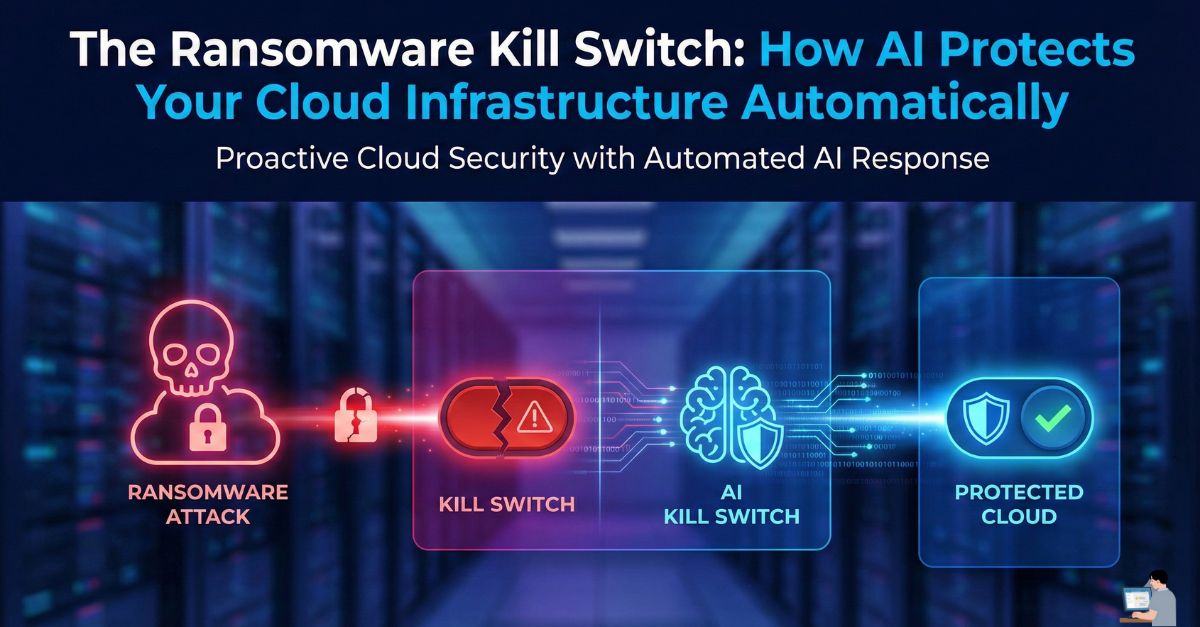
In this guide, we are going to talk heart-to-heart about the “AI Kill Switch.” We will decode how artificial intelligence acts as an autonomous immune system, showing you exactly how to protect your digital livelihood from a founder’s ultimate nightmare.
The Nightmare: Modern Cloud Exploitation
When most people imagine a cloud data breach, they picture a hacker in a dark hoodie furiously guessing passwords. That is not how it works anymore. Today, cloud exploitation is highly sophisticated, silent, and entirely automated.
Hackers do not break in; they log in.
They use stolen credentials or exploit hidden vulnerabilities in third-party software you already trust. This is known as a supply chain attack. They compromise a popular workflow automation tool, allowing them to slip past your primary firewalls and access the internal networks of thousands of companies simultaneously.
Whether you are hosting your business on AWS, Azure, or Google Cloud, the attacker’s methodology is exactly the same: infiltrate quietly, spread to other servers laterally, and encrypt absolutely everything.
Enter the Kill Switch: The AI Immune System

You simply cannot fight automated ransomware with a human IT team. By the time a human gets the alert, wipes the sleep from their eyes, and logs in to diagnose the problem, your database is already gone.
To stop modern cloud computing attacks in real-time, you must fight machines with machines.
AI does not look for known viruses (which hackers constantly change). Instead, it looks at behavior. Here is exactly how the Kill Switch protects your business:
- The Baseline: The AI learns what “normal” looks like for your specific company. It knows your server usually reads 100 files a minute and sends data to a recognized, safe IP address.
- The Anomaly: A compromised account suddenly starts encrypting 10,000 files a second and sending data overseas.
- The Kill Switch: In milliseconds, the AI network protocol engages. It instantly severs the compromised server’s connection to the internet and the rest of your cloud environment.
It isolates the infection immediately, stopping the attack dead in its tracks. Traditional cloud security builds a static wall; AI security acts as an active, aggressive immune system.
The AI Trust Dilemma: Can We Rely on Machines?
It is incredibly common for business owners to feel anxious about handing over the keys to an algorithm. You might be wondering, “Can I trust this AI not to accidentally shut down my whole company?”
The candid answer is that no system is flawless. The biggest risk with AI cybersecurity solutions is the “False Positive”—the AI panicking and shutting down a legitimate business process because it mistook a massive, routine data backup for a data theft event.
This is exactly why Cybersecurity Analysts and Cloud Architects are more important than ever. The AI does not replace your human team; it handles the millisecond-speed triage so your humans have the time and safety to handle the complex forensic investigation.
Actionable Defense: 4 Ways to Prevent Cloud Attacks Today
You do not need a massive enterprise budget to start protecting your business right now. Here are four foundational ways to secure your cloud environment today:
- Enforce Phishing-Resistant MFA: SMS text messages are easily intercepted. Force your team to use hardware keys (like a YubiKey) or secure authenticator apps.
- Implement Zero Trust Architecture: A marketing intern’s account should physically not have the permissions required to access or delete your core customer database. Restrict access to strictly what is needed.
- Automate Immutable Backups: “Immutable” means the backup cannot be deleted or altered by anyone, not even a hacker who steals your admin password. If ransomware hits, you simply wipe the server and restore the immutable backup.
- Deploy Cloud Security Posture Management (CSPM): Use automated tools to constantly scan your environments for simple, accidental misconfigurations (like a developer accidentally leaving a storage bucket set to “Public”).
🎁 Exclusive Publisher Bonuses: Advanced Security Tactics
Because I want your business to be as fortified as possible, here are two advanced, highly effective strategies you can implement to outsmart the hackers:
Bonus 1: The “Infrastructure as Code” Shield
If you manage your cloud servers manually by clicking around a dashboard, you are prone to human error—which is the number one cause of cloud breaches. Instead, manage your security using Terraform (Infrastructure as Code).
You write your security rules in code. If a hacker somehow gains access and changes your firewall rules to let themselves in, Terraform will instantly detect the change and automatically revert the firewall back to your secure, master code within seconds. It is a self-healing infrastructure.
Bonus 2: The “Honeytoken” Decoy Strategy
Create a set of fake AWS access keys and leave them sitting in your company’s internal documents or Slack channels. These keys do not actually grant access to anything, but you set an alert on them. If a hacker breaches your system, they will greedily grab these keys and try to use them. The moment they do, an invisible, silent alarm triggers, immediately notifying your AI to lock down the network before the hacker even knows they are caught.
Reclaiming Your Peace of Mind
There is no feeling quite like the sheer terror of losing control of your life’s work to a faceless extortionist.
Ransomware is a lucrative, highly organized criminal enterprise. But you do not have to be a victim. By understanding the threats, embracing AI as your 24/7 autonomous guard dog, and implementing the “Kill Switch” mentality, you completely shift the balance of power back into your hands.
You deserve to go to sleep at night knowing that if a threat breaches your perimeter at 3:00 AM, the machine will handle it.